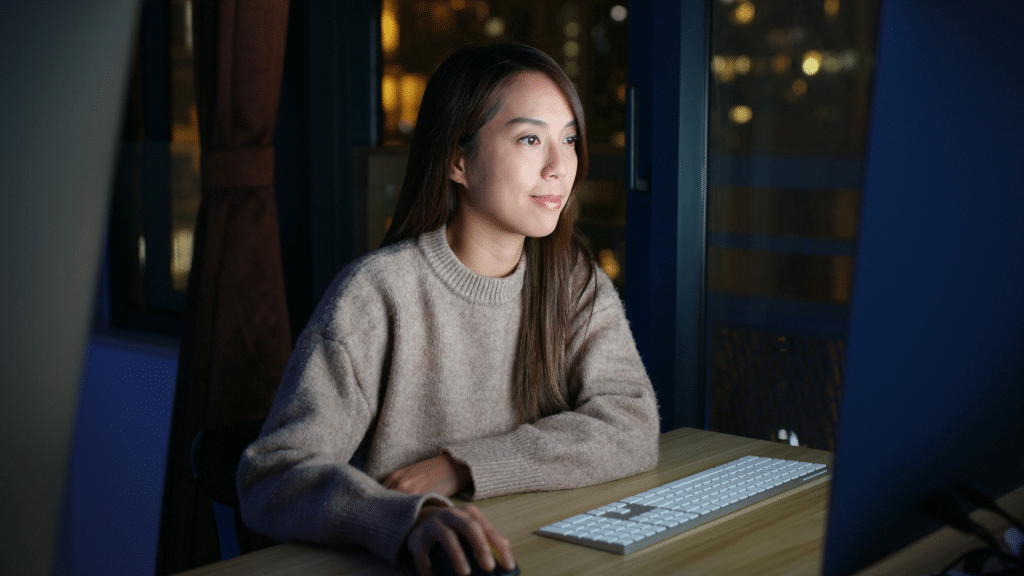
Premier Level
Managed IT Services
Adet IT Solutions emerges as a leader in the IT solutions field, delivering tech-powered, human-guided IT installation services. Our services range from project management for IT installs to enterprise IT installations, and everything in between.
Premier IT Installation Services
Choose Adet IT Solutions for all your IT installation needs, be it onsite or remotely. We provide customized IT solutions, including network hardware setup and server installation services, tailored specifically to ensure the success of your business.
01
ADVANTAGES
Navigate the complex world of IT infrastructure setup while avoiding potential risks that come with managing your businesses hardware needs.

01
Preventing System
Failures
Proactively identify and manage potential hardware issues before they lead to system failures and disrupt your business operations
02
Adherence to
Industry Standards
Avoid unnecessary complications by using industry-standard best practices for all your IT hardware and network setup needs.
03
Preparedness for
Inspections
Leverage our services to maintain inspection-ready records and ensure your business stays ahead of any compliance or audit requirements.
04
Boosted
Business Productivity
Ensure smooth business operations and protect your future earnings through quick problem-solving and ensuring your workforce has access to the IT resources they need.
05
Building Clients Confidence
Strengthen your brand’s reputation as a modern, reliable company anchored by top-tier IT systems, thanks to our professional IT setup services.
02
ATTRIBUTES
Experience Flexible & Powerful
IT Installation solutions.
No matter the scale of your IT installation needs, Adet IT Solutions is equipped to integrate the most current technologies in the most flexible and personalized approach.
- IT Installation Strategy
- Practical Roadmap aligned with the Installation Strategy
- Training initiatives to enhance IT Awareness throughout the enterprise
- Improvements or definitions in IT installation strategies, tools, and processes
- Data Center Compliance readiness review, gap analysis, and consequent action steps (following ISO 27701)
- Risk Evaluation report highlighting prioritized risks within the scope of the evaluation and providing risk mitigation recommendations
Assessments based on NIST, ISO, EIC, CIS CSC, FDA standards.
- Vulnerability Analysis to identify potential hardware issues, assess their impact, and suggest risk mitigation measures.
- Onsite Evaluations conducted by expert SMEs aimed at identifying hardware weaknesses, assessing the significance of gaps, and proposing risk mitigation measures.
- IT Infrastructure & Architecture review, providing a report that prioritizes risks within the scope covered by the review and suggesting risk mitigation measures.
IT system fortification
- ISO 27001 (Information Security Management System)
- ISO 27017 (IT Hardware Security for Cloud Services)
- ISO 27018 (Privacy for Cloud Services)
- ISO 22301 (Business Continuity)
- ISO 27701 (Privacy Management)

03
WHY CHOOSE US?
Bear in mind – security isn’t an expense, it’s a strategic investment.
A thorough IT hardware and compliance evaluation covering these three aspects offers the greatest return on your investment. Our IT installation & compliance specialists will review your design or existing setup, provide advice on how to mitigate hardware risks, and ensure adherence to standards and regulations such as the FDA or GDPR.

A deep understanding of overall
IT market trends and dynamics in various industries including manufacturing, Professional Services, Healthcare, and Construction.

Wide-ranging knowledge
of technology solutions such as AI, ML, IoT, Robotics Process Automation (RPA), Cloud, Big Data, and more

Robust facilitation
and consultation skills
Exceptional communication skills
spanning technical, managerial, and executive levels
15 Things Hackers Don 't Want You To Know
The guide, “15 Things Hackers Don’t Want You to Know,” is a must-read for businesses seeking to enhance their cybersecurity. It offers actionable steps to defend against cyber threats, covering essential topics from password security to incident response plans. By downloading this concise guide, you equip yourself with practical strategies to safeguard your business in the increasingly complex landscape of cyber threats.
